By Fredrik Brattstig @virtualbrat
YES!!!
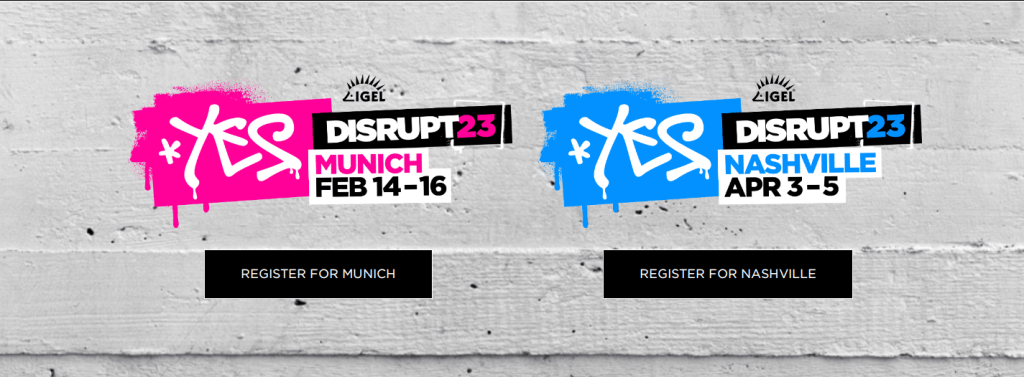
IGEL is gathering the EUC ecosystem again! And YOU should be there!
Top vendors are all together in one place, at the same time! We will see representatives from Microsoft, Citrix, VMware, HP, Lenovo, LG, and many many more.
There will be breakout sessions, tech boot camp, panel discussions and key notes from industry-leading experts and you know what, maybe I even will host a tech breakout session 🙂
To all my readers of virtualbrat.com, I can offer a discount code, you just need to pick and choose if you want to attend IGEL Disrupt in Munich, EMEA or in Nashville, US.
Make sure that you sign up before the the 31st of December 2022 to get the early-bird discount + virtualbrat.com discount on top! From the 1st of January, regular attendeee fee will apply, though, you will still get the virtualbrat.com discount added!
Let’s meet in Munich! :

Let’s meet in Nashville:

See you at the events!
/Fred

